Operational Risk Mapping.
Operational Risk Mapping

4
1. Concept of Operational Risk Mapping
Operational Risk Mapping is the structured process of:
- Identifying operational risks within an organization
- Mapping them to business processes, systems, people, and third parties
- Assessing their impact, likelihood, and interdependencies
It is a core component of:
- Enterprise Risk Management (ERM)
- Operational resilience frameworks
- Regulatory compliance (e.g., Basel III, FCA/PRA rules)
2. Meaning of Operational Risk
Operational risk is defined (Basel framework) as:
“The risk of loss resulting from inadequate or failed internal processes, people, systems, or external events.”
Examples include:
- IT failures
- Fraud
- Cyberattacks
- Human error
- Third-party disruptions
3. Objectives of Risk Mapping
(a) Risk Identification
- Detect vulnerabilities across operations
(b) Risk Visualization
- Use tools like:
- Heat maps
- Process flow diagrams
(c) Dependency Analysis
- Understand how risks propagate across systems
(d) Regulatory Compliance
- Meet requirements under:
- FCA/PRA
- Basel Committee guidelines
4. Key Components of Operational Risk Mapping
(i) Business Process Mapping
- Identify critical workflows
- Break down:
- Inputs
- Outputs
- Dependencies
(ii) Risk Identification
- Map risks to each process stage:
- Process failures
- System breakdowns
- Human errors
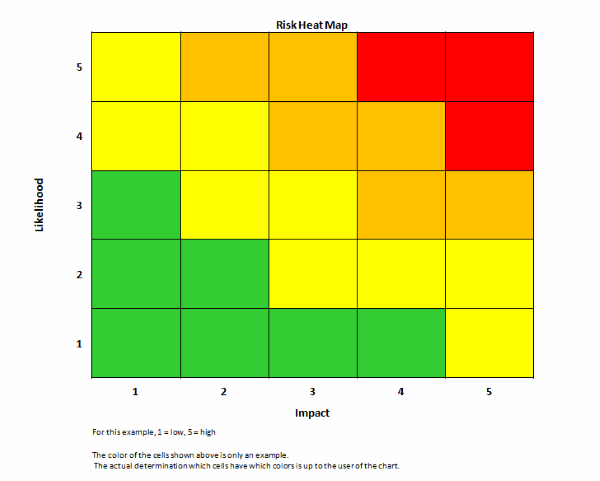
(iii) Risk Assessment
- Evaluate:
- Likelihood
- Impact
Often represented through risk matrices.
(iv) Control Mapping
- Identify:
- Existing controls
- Gaps in controls
(v) Risk Ownership
- Assign responsibility to:
- Departments
- Senior managers
(vi) Third-Party Mapping
- Identify dependencies on:
- Vendors
- Outsourced services
5. Methodologies Used
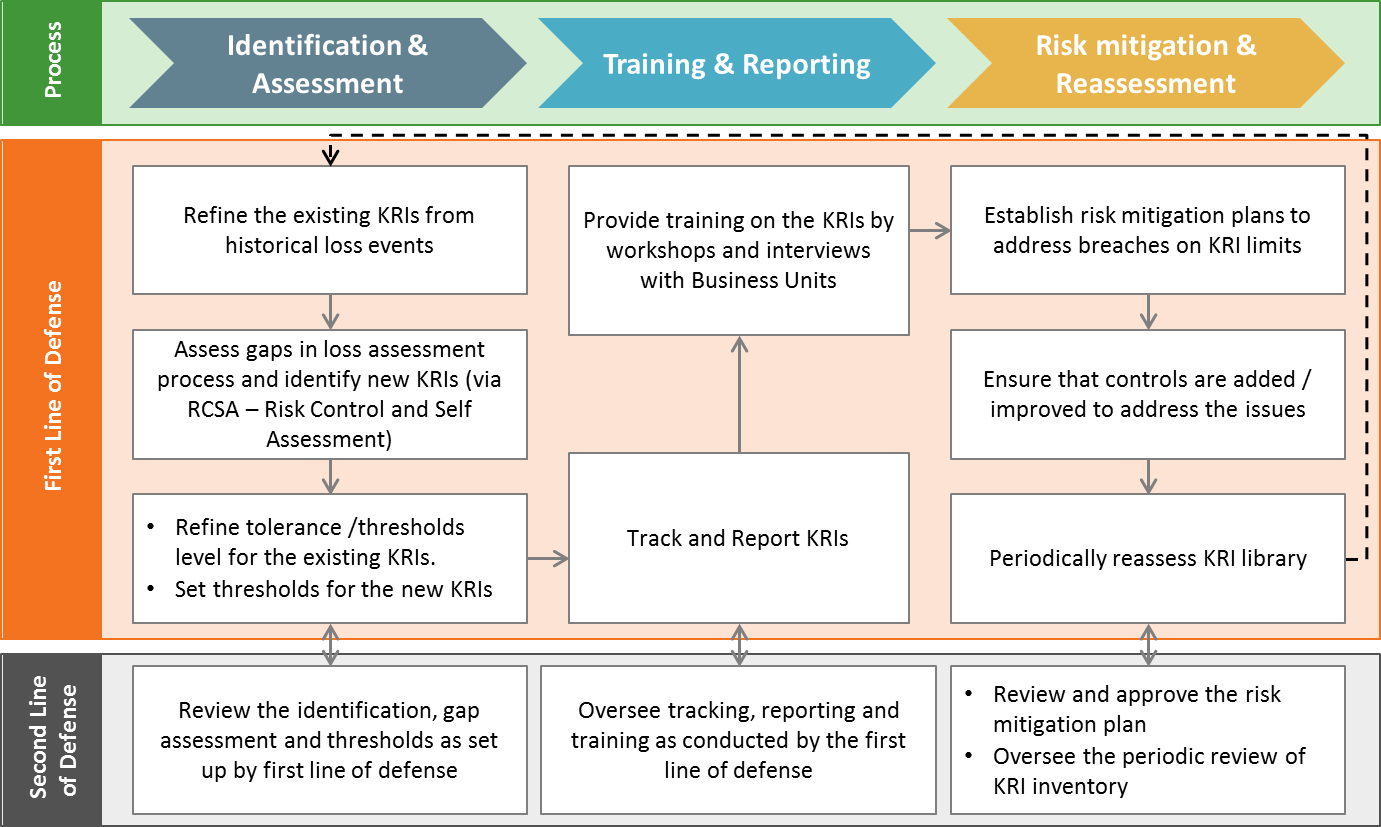
(a) Risk and Control Self-Assessment (RCSA)
- Internal evaluation of risks and controls
(b) Key Risk Indicators (KRIs)
- Metrics used to monitor risk exposure
(c) Scenario Analysis
- Simulate extreme but plausible events
(d) Process Mining
- Use data analytics to identify inefficiencies and risks
6. Legal and Regulatory Importance
Operational risk mapping is essential for:
- Demonstrating compliance with regulatory requirements
- Avoiding regulatory penalties
- Supporting litigation defense (showing due diligence)
Regulators expect:
- Clear documentation
- Regular updates
- Integration with governance frameworks
7. Case Laws and Legal Precedents
While not always labeled as “risk mapping” cases, the following illustrate failures in operational risk identification and control:
(1) FCA v. RBS (NatWest IT Failure, 2012)
- System failure disrupted banking services
Outcome:
£56 million fine
Relevance:
Failure to properly map and manage IT risks.
(2) FCA v. Tesco Bank (2018 Cyberattack)
- Cyberattack exploited system vulnerabilities
Outcome:
£16.4 million fine
Relevance:
Inadequate identification of cyber risk exposure.
(3) Barings Bank Collapse (1995)
- Rogue trading by Nick Leeson
Relevance:
- Failure to map:
- Operational controls
- Segregation of duties
(4) JP Morgan Chase “London Whale” Case (2012)
- Trading losses due to poor risk controls
Relevance:
Inadequate risk mapping of complex financial activities.
(5) Equifax Data Breach (2017)
- Failure to patch known vulnerabilities
Relevance:
Weak risk identification and mapping of IT systems.
(6) Capital One Data Breach (2019)
- Cloud misconfiguration
Relevance:
Failure in mapping third-party and cloud risks.
(7) Target Data Breach (2013) (Additional)
- Breach via third-party vendor
Relevance:
Highlights importance of third-party risk mapping.
8. Practical Challenges
(a) Complexity of Modern Systems
- Interconnected digital ecosystems
(b) Data Silos
- Lack of integrated information
(c) Dynamic Risk Environment
- Rapidly evolving cyber threats
(d) Human Factors
- Errors and misconduct
9. Risk Mitigation Strategies
(i) Integrated Risk Frameworks
- Align operational risk with:
- Cyber risk
- Compliance risk
(ii) Technology Adoption
- Use:
- Risk management software
- AI-driven analytics
(iii) Continuous Monitoring
- Real-time dashboards
(iv) Strong Governance
- Board-level oversight
(v) Third-Party Risk Management
- Vendor due diligence
- Contractual safeguards
10. Relationship with Operational Resilience
Operational risk mapping is a foundation of operational resilience:
- Helps identify critical services
- Supports impact tolerance setting
- Enables scenario testing
11. Conclusion
Operational risk mapping is a critical tool for modern organizations, especially in highly regulated sectors like finance:
- It enables proactive risk identification
- Strengthens internal controls and governance
- Supports regulatory compliance and legal defense
Case law demonstrates that failure to properly map risks can result in:
- Financial losses
- Regulatory penalties
- Reputational damage
As organizations become more complex, dynamic and technology-driven risk mapping will be essential for sustainable operations.




comments